Key Takeaways:
-
AI's Double-Edged Sword: While AI offers potential for converting vulnerable code to Rust, it also introduces new complexities and potential for oversimplification of critical tasks.
-
"Idiomatic" Imperative: AI-generated code often lacks the human-centric "idiomatic" qualities crucial for long-term maintainability and readability by expert Rust developers.
-
Talent Chasm: The scarcity of Rust experts poses a significant challenge for monitoring and maintaining large volumes of AI-translated code, potentially shifting the vulnerability from creation to upkeep.
-
Funding Fissures: Ambitious government funding for initiatives like the "Great Refactor" remains uncertain, pushing proponents towards a potentially less aligned commercial sector.
-
No Silver Bullet: Experts caution against viewing AI as a complete solution, emphasizing its current limitations in guaranteeing robustness and preventing subtle errors or "hallucinations" in complex code translation.
Is AI's Promise of Rust Conversion a Cybersecurity Pipe Dream?
[FEATURED]
The digital realm is a landscape riddled with vulnerabilities, largely thanks to decades of software built on foundations like C and C++. These languages, while powerful, offer developers manual control over memory, a freedom that has directly led to an estimated 70 percent of all software vulnerabilities: memory safety exploits. The emergence of Rust, a language designed to offer C/C++ performance with integrated memory safety, presents a compelling alternative. Now, with the rapid advance of AI coding tools, a new, audacious vision has taken hold: the automatic conversion of vast swathes of vulnerable legacy code into Rust. But is this a genuine revolution or an overhyped panacea threatening to trade one set of problems for another?
The Institute for Progress's "Great Refactor" initiative, championed by project lead Herbie Bradley from the University of Cambridge, proposes a U.S. government-funded "Focused Research Organization." Their ambitious goal: convert 100 million lines of C/C++ open-source code to Rust by 2030, projecting a $100 million investment could prevent billions in cyberattack losses. On paper, it sounds like an irresistible offer, leveraging AI's newfound prowess to tackle tasks previously deemed "too expensive or time-consuming."
However, the very nature of software engineering, particularly in security-critical domains, resists simplistic solutions. While Bradley expresses a "bullish" outlook, believing AI will allow for Rust versions of any major library within five years, the allure of a "one-shot" fix for vulnerabilities, rather than the painstaking "case-by-case" bug squashing, is undeniable, particularly for the "long tail" of under-maintained open-source projects. Yet, the devil, as always, is in the details – and the code.
The Idiosyncrasies of "Idiomatic" Code
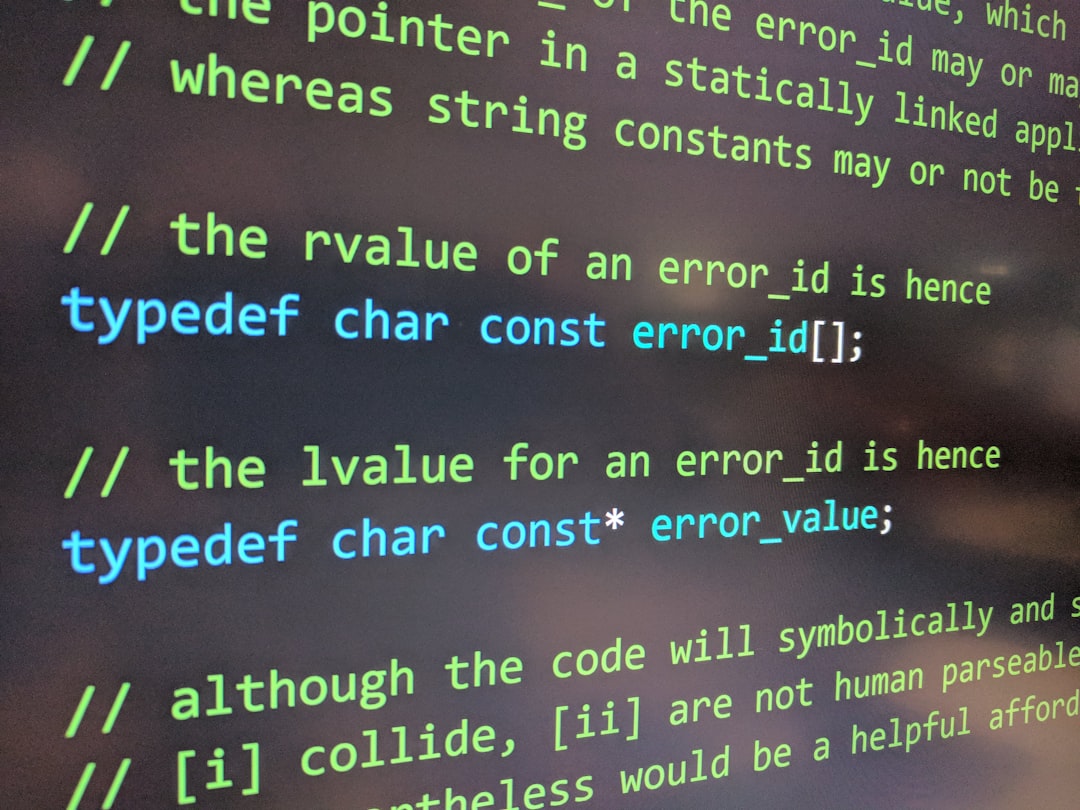
The U.S. Defense Advanced Research Projects Agency's (DARPA) "Translating All C To Rust" (TRACTOR) program, launched in 2024, directly grapples with these complexities. Program manager Dan Wallach emphasizes a hybrid approach, combining generative AI with traditional code analysis. While acknowledging AI's promise, he notes the decades of research into "writing software to analyze other software" cannot be discarded.
A crucial metric for TRACTOR's funded teams goes beyond mere correctness and performance: "idiomatic" Rust. This refers to code that adheres to the language's best practices, leveraging its unique features and paradigms in a way a skilled human Rust programmer would. Wallach asks: "does the code look the way a skilled Rust programmer would have built it from scratch?"
This "idiomatic" quality is not a stylistic flourish; it's fundamental to long-term maintainability. Josh Triplett, an open-source developer contributing to the Rust project, warns that AI-translated code is "likely to end up with code that is difficult for a human to maintain compared to what was manually translated." While he welcomes efforts to convert code to Rust, Triplett cautions against widespread adoption by teams not already adept at managing AI-assisted codebases, especially for critical, widely used open-source libraries. The risk, he explains, is that AI "will never be a silver bullet for AI being 100 percent robust against doing the wrong thing, whether it is by hallucinating or by not understanding the assignment." This directly contradicts the "one-shot" vulnerability fix ideal, suggesting a potential for new, more subtle vulnerabilities introduced by automated translation.
The Talent Chasm and Maintenance Burden
Even assuming a perfectly "idiomatic" translation, the human element presents another formidable barrier. Jessica Ji, a senior research analyst at Georgetown University's Center for Security and Emerging Technology, points out the significant disparity in developer bases: "There are a lot fewer Rust experts out there than C/C++ experts, so the number of expert eyes on the codebase(s) will likely be fewer." This creates a daunting maintenance challenge. A massive influx of AI-generated Rust code, however secure in its initial translation, still requires ongoing monitoring, debugging, and feature development – tasks for which the pool of qualified individuals is alarmingly shallow. This could inadvertently shift the security burden from code creation to code maintenance, creating new points of failure.
Funding Fissures and Commercial Realities
Perhaps the most immediate hurdle, however, is securing the colossal funding required. Ji views convincing the U.S. government to back the "Great Refactor" at its envisioned scale as a "biggest barrier." She suggests a more pragmatic initial step: soliciting private sector funding for a proof-of-concept, noting that "AI companies are particularly incentivized to show off their models' capabilities."
Bradley, too, is exploring similar avenues, acknowledging that a significant portion of vulnerable code resides in private companies and critical infrastructure providers, making a commercial venture potentially more sensible. This pivot highlights a fundamental tension: while the initiative aims to bolster public good cybersecurity, its financing might ultimately rest on commercial interests, whose motivations may not always perfectly align with the rigorous, slow, and expensive process of securing the "long tail" of critical but unglamorous open-source infrastructure.

Public Sentiment
Optimism regarding AI's potential for code transformation is tempered by a healthy dose of skepticism regarding its practical application. Herbie Bradley's "bullish" view acknowledges cost and time savings, yet experts like Dan Wallach, from DARPA's TRACTOR program, insist on a "hybrid approach" mixing AI with "decades of research into writing software to analyze other software." Wallach critically highlights the challenge of creating "idiomatic" Rust—code that mirrors human best practices—a concern echoed by Josh Triplett, who warns AI-translated code may prove "difficult for a human to maintain." Triplett further cautions against AI as a "silver bullet," citing risks of "hallucinating or by not understanding the assignment." Jessica Ji points to the critical human factor: the acute scarcity of Rust experts to maintain AI-generated code, and the significant hurdle of securing government funding for such an ambitious undertaking, suggesting a more realistic private sector approach for initial proof-of-concept.
Conclusion: Caution Amidst the Hype
The vision of an AI-powered "Great Refactor" transforming the cybersecurity landscape is undoubtedly ambitious and, in some respects, appealing. Yet, a critical examination reveals a complex tapestry of technical, human, and financial challenges. From the subtle art of "idiomatic" code to the stark realities of talent scarcity and funding uncertainties, the path to wholesale AI-driven Rust conversion is fraught with obstacles. While AI's role in software development will undoubtedly grow, caution, skepticism, and a realistic understanding of its current limitations are paramount. Rushing into a "silver bullet" solution risks creating new problems faster than it solves old ones, leaving us with a digitally "refactored" future that is perhaps more fragile, rather than fundamentally more secure.