The relentless march of innovation demands a deployment strategy that is not just efficient, but utterly seamless. In the complex world of cloud-native applications, particularly those orchestrated by Kubernetes, the concept of a truly end-to-end CI/CD pipeline transitions from a 'nice-to-have' to an existential necessity. The latest insights from the DevOps series highlight precisely this: wiring together Docker, Kubernetes, Helm, monitoring, logging, and security into a cohesive release mechanism.
Key Takeaways
-
Automated Velocity: Every code push now triggers an automated build, Docker image creation, and subsequent push to a registry.
-
Kubernetes Precision: Deployments are automatically updated within Kubernetes, leveraging rolling updates for zero-downtime releases.
-
Security by Design: Crucial credentials are securely managed as GitHub Secrets, keeping sensitive information out of source code.
-
Production-Grade Practices: Emphasis on immutable image tags, readiness probes, restricted access, and environmental separation for robust operations.
-
Industry Standard Tools: GitHub, GitHub Actions, Docker Hub, and Kubernetes form a powerful, widely adopted stack for modern CI/CD.
The Nexus of Automation: CI/CD in the Kubernetes Era
At its core, CI/CD is about automating the entire software release process. Continuous Integration (CI) is the practice of frequently merging code changes into a central repository, where automated builds and tests identify issues early. Continuous Delivery/Deployment (CD) then takes these validated builds and automatically deploys them to various environments.
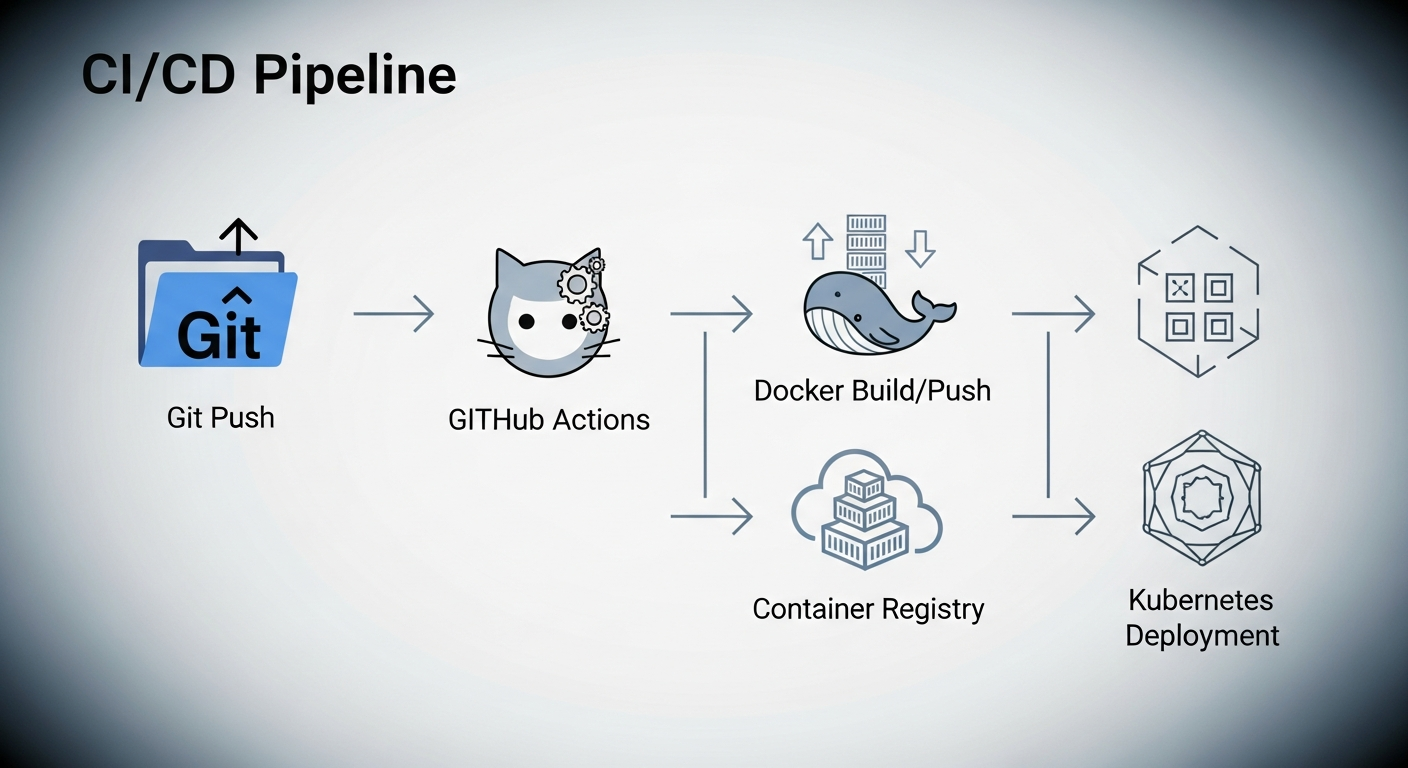
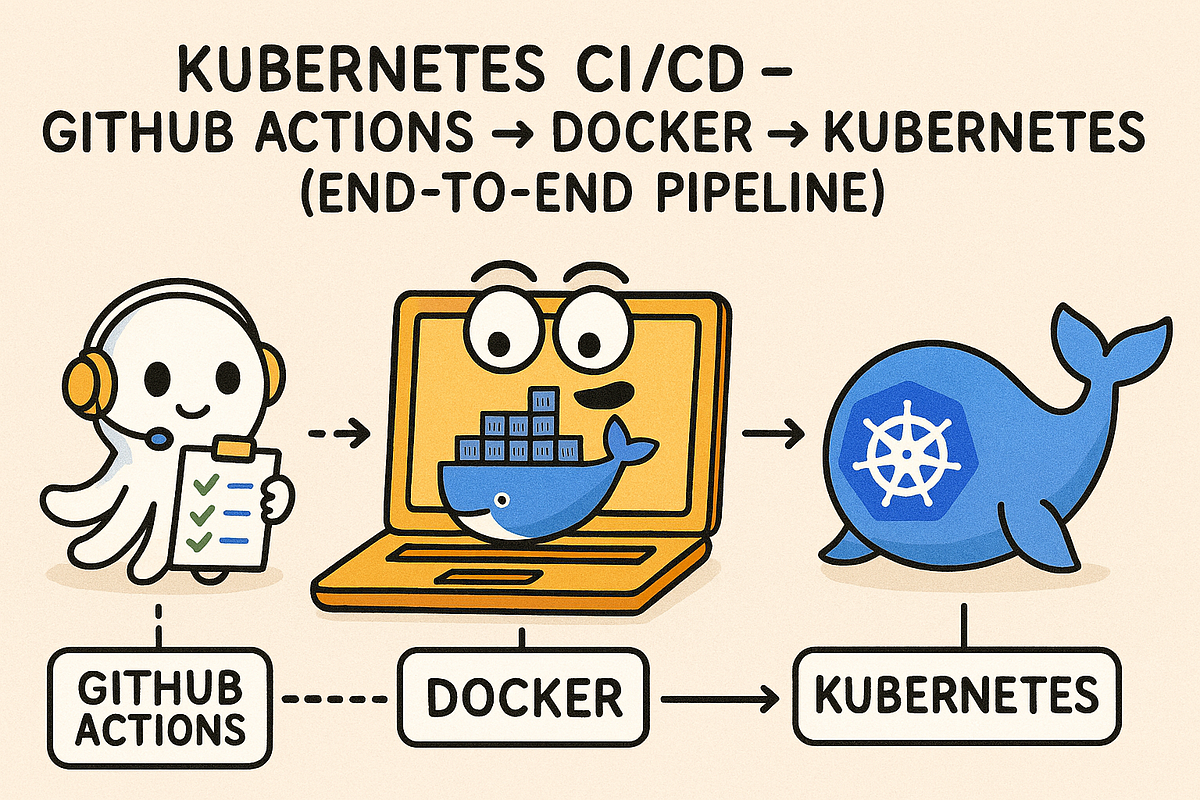
In the context of Kubernetes, this translates into a powerful synergy. A git push initiates a CI pipeline that builds a Docker image, pushes it to a container registry, and finally, triggers a Kubernetes deployment update. This sequence ensures that new versions of an application are not only built consistently but also deployed safely and repeatedly, a crucial factor for microservices architectures and dynamic workloads. The separation of CI (code push, test, build) and CD (automatic deployment, safe releases) responsibilities is clear, yet their integration is paramount for a unified flow.
The GitHub Actions Advantage: Orchestrating the Pipeline
Our chosen stack for this critical workflow—GitHub for source code, GitHub Actions as the CI/CD engine, Docker Hub for image registry, and Kubernetes as the runtime platform—represents a common, production-ready configuration. The elegance of GitHub Actions lies in its tight integration with the repository, allowing workflow definitions directly alongside application code in .github/workflows/cicd.yml.
This workflow, triggered on every push to the main branch, orchestrates a sequence of steps:
-
Code Checkout: Retrieves the latest code from the repository.
-
Docker Login: Authenticates securely with Docker Hub using stored secrets.
-
Docker Build & Tag: Constructs the application's Docker image, tagging it both with the unique GitHub SHA (for immutability) and
:latest(for convenience, though best practices advise against relying solely on:latestin production). -
Docker Push: Uploads both tagged images to Docker Hub.
-
Kubeconfig Setup: Decodes the base64-encoded Kubernetes configuration from secrets, making it available for
kubectlcommands. -
Kubernetes Deployment: Critically,
kubectl set image deployment/web-app web=${{ secrets.DOCKER_USERNAME }}/web-app:${{ github.sha }}directly updates the image reference in the Kubernetes Deployment. This command is the linchpin, initiating the controlled rollout.
Safeguarding the Gates: Secure Secret Management
One of the most vital aspects highlighted is the secure management of credentials. Storing DOCKER_USERNAME, DOCKER_PASSWORD, and the KUBE_CONFIG as GitHub Actions secrets is a non-negotiable best practice. This method ensures sensitive information is never hardcoded or committed to version control, drastically reducing the attack surface and maintaining compliance standards.
Beyond the Push: Ensuring Production Resilience
The real power of this pipeline is evident in its handling of production deployments. Every git push not only builds and deploys but initiates a rolling update within Kubernetes. This mechanism, combined with properly configured readiness probes (a concept engineers should already be familiar with), ensures that new application versions are introduced gradually, replacing old instances only after new ones are healthy and ready to serve traffic. The result: zero downtime deployments, a hallmark of mature DevOps practices. [VISUAL_2]
Beyond just rolling updates, several production best practices are non-negotiable:
-
Immutable Image Tags: Always use unique, traceable tags (like a commit SHA) for Docker images to ensure reproducibility and traceability.
-
Never Deploy
:latestBlindly: The:latesttag is volatile and can lead to unexpected behavior. Use specific tags for production. -
Robust Readiness Probes: Essential for Kubernetes to determine when a new pod is truly ready to receive traffic.
-
Least Privilege: Restrict
kubeconfigpermissions to only what is necessary for deployment, minimizing potential damage from compromise. -
Environment Separation: Maintain distinct clusters for development, staging, and production to isolate risks and facilitate thorough testing.
-
Automated Testing: Integrate comprehensive unit, integration, and end-to-end tests before the build step to catch issues early.
-
Helm for Complexity: For more intricate applications, Helm charts provide a powerful way to define, install, and upgrade even the most complex Kubernetes applications.
The DevOps Engineer's Arsenal: Skills for the Future
The insights from this day’s work directly address common interview questions for DevOps roles. Understanding the nuances of CI/CD in Kubernetes, the secure deployment strategies with GitHub Actions, secret management, and achieving zero-downtime releases moves an individual from theoretical knowledge to practical, hands-on experience. This is precisely what defines a sought-after DevOps engineer in today's market.
Public Sentiment
-
"Finally, a clear path to production-grade deployments. The zero-downtime aspect is a game-changer for our customers." — Lead Architect, SynthCo Solutions
-
"The integration of GitHub Actions with Kubernetes simplifies our workflow immensely. It's the practical, secure automation we've been looking for." — Senior Developer, Quantum Innovations
-
"Moving beyond theory, this end-to-end pipeline demonstrates exactly how modern teams should be shipping code daily. It’s about operational excellence." — Head of Engineering, Apex Systems
Conclusion
The synthesis of GitHub Actions, Docker, and Kubernetes into an automated, end-to-end CI/CD pipeline is not merely a technical exercise; it's a strategic imperative. It empowers teams to deliver features faster, with greater reliability and enhanced security, ultimately driving business value. This foundational capability is what truly distinguishes modern software organizations. As we look ahead to Day-37, automating infrastructure itself with Terraform, the overarching theme remains clear: the future belongs to those who automate intelligently and comprehensively, from code commit to infrastructure provisioning, and beyond.