The Allure of the Homebrew Security Device
The digital age has ushered in a deluge of passwords, PINs, and authentication keys, each guarding a piece of our digital lives. For many, the idea of entrusting these critical credentials to a third-party application or cloud service feels counterintuitive, sparking a desire for absolute control. This sentiment often leads individuals down the path of creating bespoke hardware solutions – devices designed to physically store and manage passwords, disconnected from the internet and perceived vulnerabilities of software. Our subject, a custom-built password keeper, was born from this very impulse: a small, self-contained unit promising an impenetrable, offline vault for digital keys. The initial vision was clear and compelling: a simple, tactile interface, local storage, and the peace of mind that comes from owning every layer of its security.
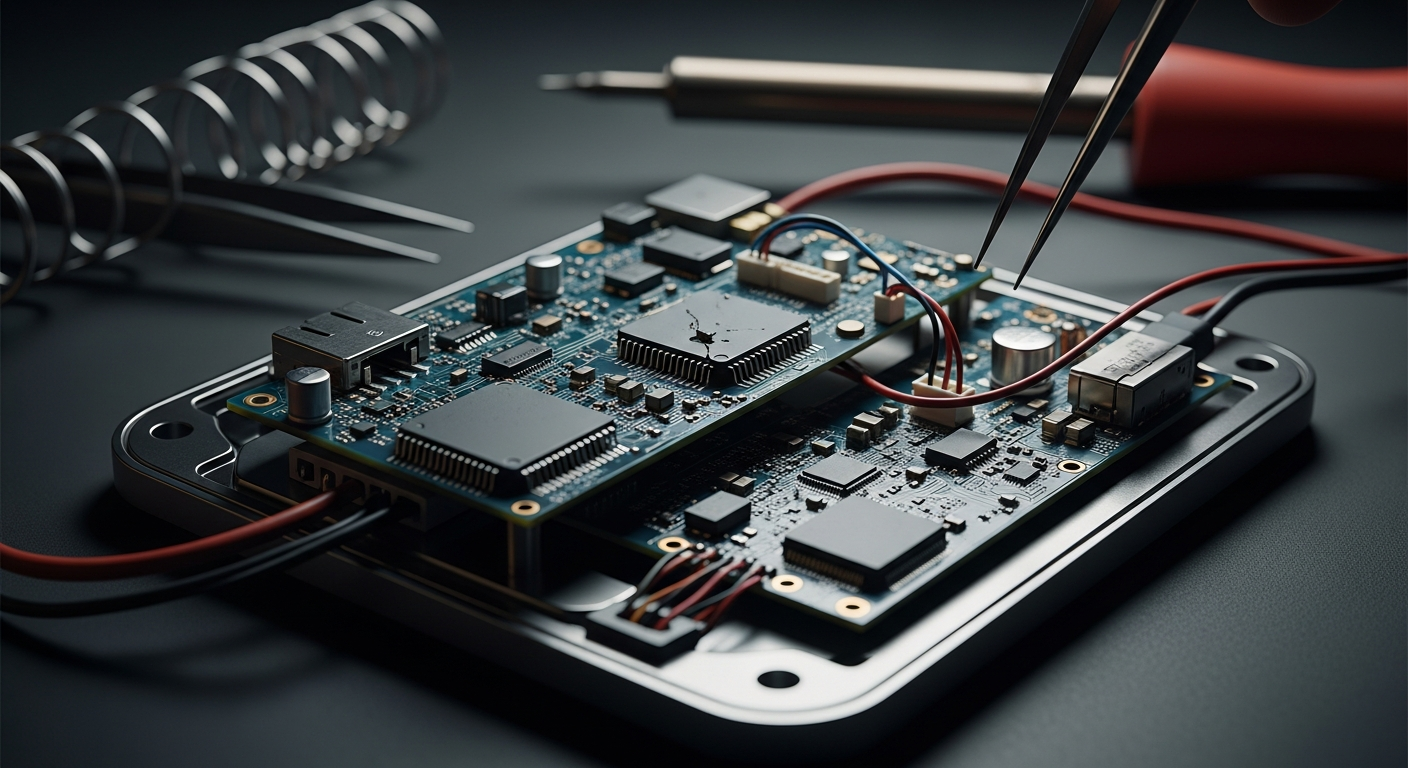
Disassembly and Discovery: The Autopsy Begins
The device arrived in our lab, a compact enclosure with a keypad and a small display, testament to its creator's ambition. Externally, it appeared robust, if a little rough around the edges – the hallmark of many passionate DIY projects. Our "autopsy" began not with destruction, but with meticulous documentation, carefully opening the casing to reveal its inner workings. What lay beneath the surface was a labyrinth of wires, custom PCBs, and off-the-shelf microcontrollers. Initial inspection revealed a curious blend of elegant solutions and glaring oversights. While the core functionality seemed present, the method of data storage and protection immediately raised red flags. Data, purportedly encrypted, was stored on a readily accessible flash memory chip, lacking the physical tamper-detection mechanisms one would expect from a security-focused device. Further probing revealed a custom firmware, riddled with inefficiencies and, more critically, several insecure coding practices that made it vulnerable to simple bypass techniques.
The Perils of Unchecked Ingenuity
The creator's ingenuity was evident in many aspects – the bespoke keypad matrix, the power management solutions, and the compact form factor. However, this same ingenuity, unchecked by formal security audits or industry best practices, became its Achilles' heel. The device relied heavily on obscurity for its security, a principle notoriously unreliable in practice. The encryption algorithm, while custom, was weakly implemented and susceptible to brute-force attacks given sufficient time and access to the device. Moreover, the physical security was minimal; the case could be opened with standard tools, providing direct access to the data storage. The most critical flaw, however, lay in its operational logic: a 'master reset' function, intended for convenience, inadvertently created a backdoor, allowing any sufficiently determined individual with physical access to wipe and potentially reconstruct elements of stored data, or worse, gain access to partial unencrypted fragments during the process. This highlights a fundamental challenge in DIY security: bridging the gap between functional design and hardened, resilient security.
Lessons from the Lab Bench
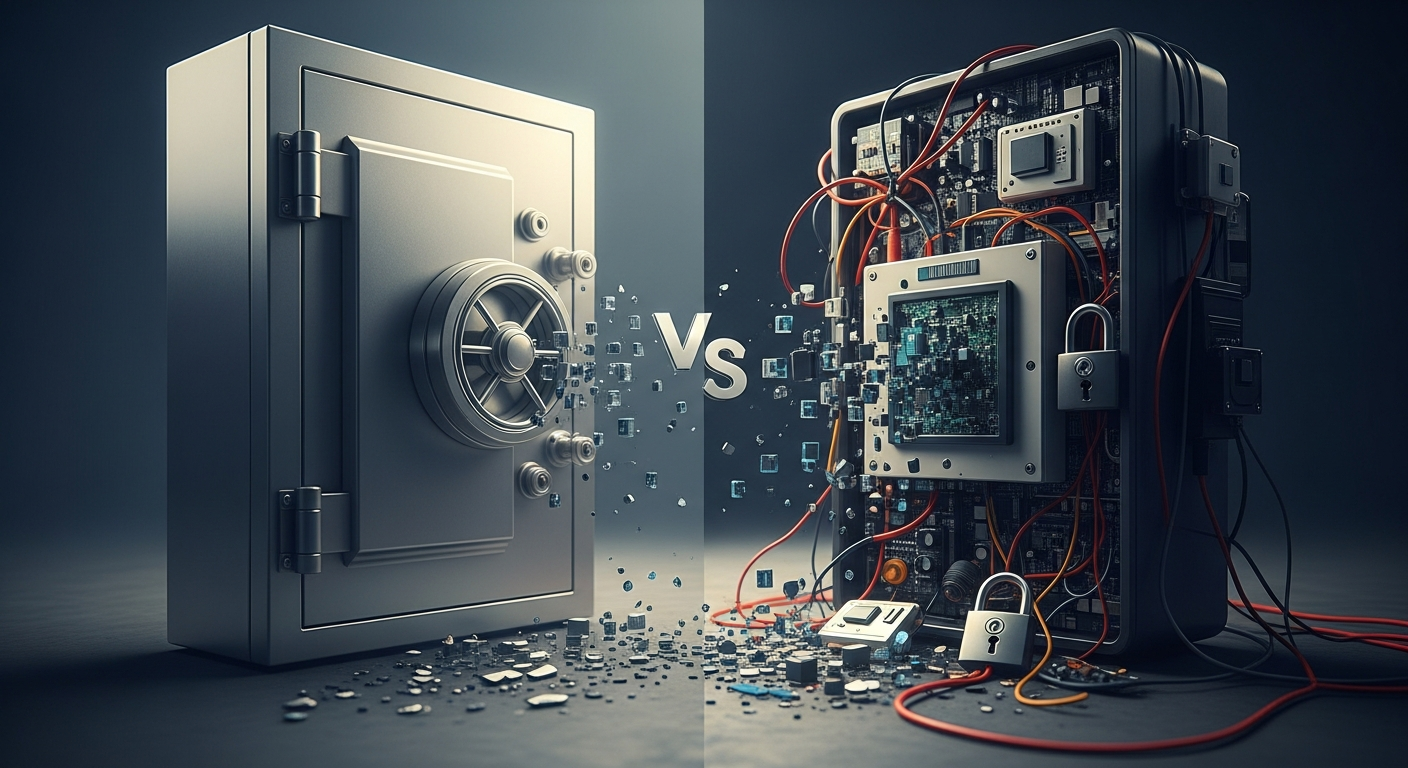
This password keeper autopsy serves as a stark reminder that security is a holistic challenge, not merely a feature. While the ambition to create personal, secure hardware is commendable, it often underestimates the sheer depth of expertise required to build truly robust systems. From cryptographic primitives to supply chain integrity, and from physical tamper resistance to secure boot procedures, each layer demands specialized knowledge. For the average user, this implies a crucial distinction: convenience does not equal security, and self-sufficiency does not bypass the need for rigorous, peer-reviewed engineering. This device was a labor of love, but ultimately, its love for clever hacks overshadowed the uncompromising discipline required for genuine security.
Key Takeaways:
-
Complexity Creep: Simple ideas often evolve into complex systems with hidden vulnerabilities.
-
DIY Security Risks: Personal security solutions require professional-grade diligence in design and implementation.
-
The Illusion of Control: Building your own device doesn't automatically equate to superior security or robustness.
-
Importance of Robust Design: Even non-critical components can lead to catastrophic failures in a system.
-
Learning from Failure: Every hardware "autopsy" provides invaluable insights for future development and user awareness.
Public Sentiment
"Fascinating, yet terrifying," commented one reader on a tech forum. "It really makes you think twice about trusting any homemade security solution." Another user pondered, "While I admire the creator's spirit, this perfectly illustrates why established security products go through such rigorous testing. It's a humbling lesson for anyone considering a similar DIY project." The consensus across various platforms suggests a mix of admiration for the ambition, coupled with a renewed sense of caution regarding the complexities of true digital security.
Conclusion
The autopsy of this custom password keeper device is more than just a peek into a failed project; it's a profound case study in the nuances of hardware security. It underscores that while innovation is vital, it must be tempered with robust engineering principles, especially when dealing with something as sensitive as personal credentials. For developers and users alike, this narrative serves as a critical reminder: in the delicate dance between clever design and unyielding security, thoroughness and adherence to established best practices must always take precedence over shortcuts or perceived simplicity. The lessons learned here echo far beyond this single device, influencing how we approach personal data protection in an increasingly complex digital world.